Trace Leaks.
Prove Origin.
Stop Piracy.
De-anonymize massive digital leaks using our cutting-edge invisible cryptographic pixel signatures. Your intellectual property is actively tracked the very second it visually renders on a rogue domain.
We specialize deeply in tracing video origins through the most intricate and sophisticated offshore distribution networks.
Effectively tracing video leaks requires moving decisively beyond sluggish, reactive takedown notices to actively combat hostile digital landscapes:
- Defeat Piracy Rings: Protect high-value pre-release content from sophisticated organized threats.
- Sub-Pixel Embedding: Utilize proprietary technology directly inside broadcast encoders.
- Chain of Custody: Maintain an unbroken mathematical link back to origin.
- Proactive Extraction: Stop revenue leakage through proactive enforcement protocols.
The Investigation Protocol
How our algorithmic engines execute flawlessly to protect your multi-million dollar content expenditures.
Cryptographic Injection
Secure content tracking begins with mathematically robust identity injection - embedding unique identifiers directly into the media structure itself.
- Immutable Bonding: Permanently binds identity to media.
- Deep Structural Injection: Embedded within frame geometry.
- Tamper Resistant: Cannot be removed by common transformations.
- Rapid Extraction: Identity retrieved instantly.
Advanced forensic watermarking ensures robust, imperceptible signatures embedded directly into media assets.
Global Asset Tracking
Our distributed infrastructure continuously monitors and tracks media across global platforms in real time.
- Persistent Optical Scanning: Detects visual fingerprints.
- Private Server Infrastructure: Fully controlled environment.
- Rapid Interception: Stops leaks early.
- Silent Metadata Capture: No external alerts triggered.
Irrefutable Extraction
AI-driven analytics trace leaks back to their exact origin with mathematically verifiable certainty.
- Definitive Proof: Verifiable origin tracking.
- Standardized Evidence: Legal-ready reports.
- Absolute Non-Repudiation: No denial possible.
- Eliminate Blindness: Full operational visibility.
Source file not required for identification.
Deterministic mathematical proof for legal use.
Enterprise Scale tracing
Uncompromising Video Tracing Scale
Tracing video effectively at a global scale requires an infrastructure capable of handling petabytes of unstructured visual data in real-time. Here is how Webkyte redefines the forensic metadata landscape through sheer computational dominance and unprecedented integration methodologies natively aligned with global broadcasting standards.
Dynamic Watermark
Shifting
To stay ahead of advanced attempts to erase embedded signatures, our architecture uses dynamically shifting watermark patterns across keyframes. This makes recognition-based removal far more difficult and helps preserve traceability even after aggressive visual manipulation.
Zero-Latency Live
Encoding
High-value live broadcasts require forensic identity injection without delay. Our low-level encoding workflow applies the required digital signatures in real time at the ingestion stage, helping preserve stream quality while supporting immediate traceability.
Automated Takedown
Pipelines
Once forensic evidence is collected and verified, automated enforcement workflows can accelerate the response. Our platform supports structured takedown pipelines that help remove infringing sources quickly and reduce the time between detection and action.
How Leak Tracing Works
Our technology uses a two-phase approach: watermark injection at distribution and watermark detection when leaks occur.
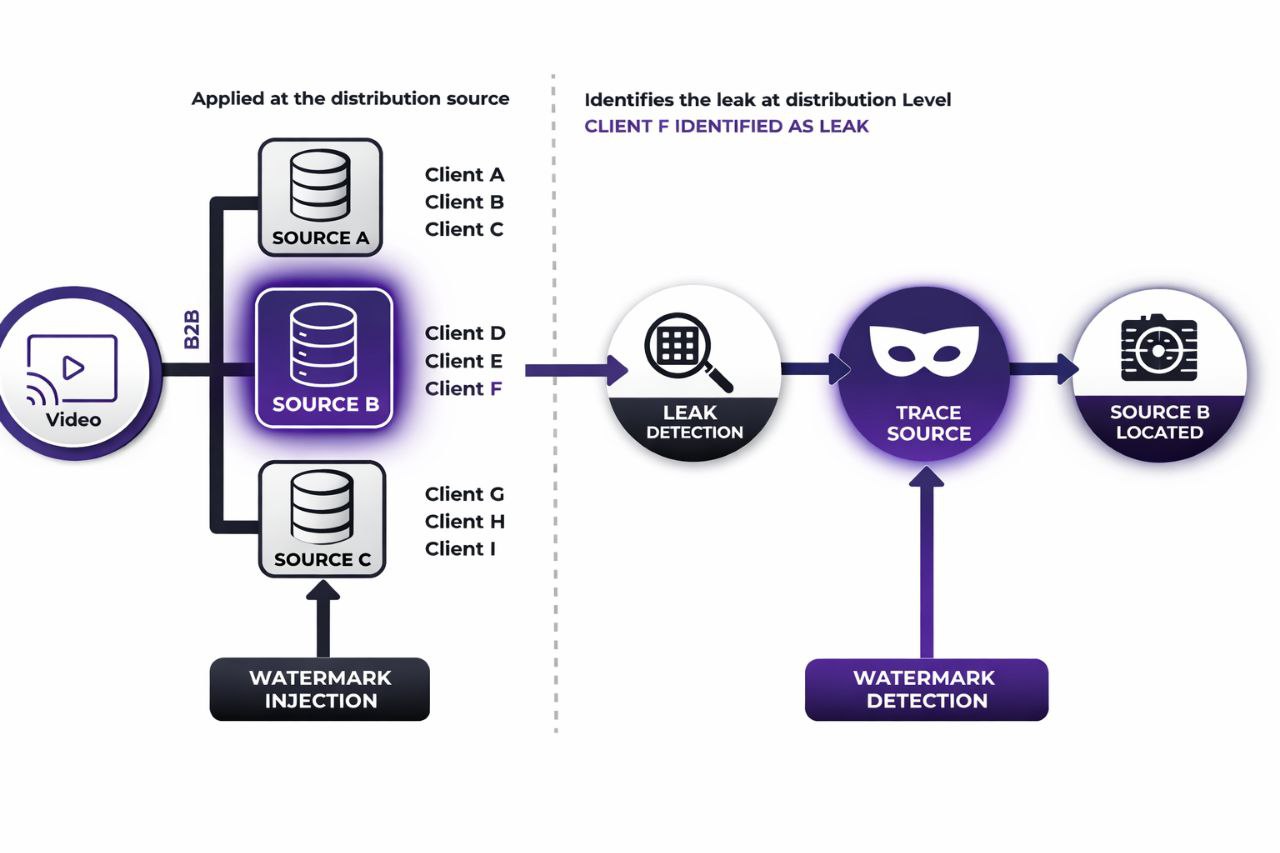
Watermark Injection
Unique watermarks are applied at the distribution source (Source A, B, C) for each client group. Each source gets a distinct identifier.
Piracy Detection
When leaked content is discovered on piracy sites or unauthorized platforms, our system automatically scans and analyzes it.
Watermark Reveal
The invisible watermark is extracted and decoded, revealing which distribution source the content came from.
Source Identification
The exact client (e.g., Client F from Source B) is identified as the leak source, providing actionable evidence.
Why Leak Tracing Matters
Content leaks cost businesses millions in lost revenue and damaged relationships. Leak tracing gives you the power to stop leaks at their source.
- Streaming PlatformsIdentify which distribution partner or region is leaking pre-release content or exclusive shows.
- Film StudiosTrack screeners sent to critics, awards voters, or press to find the source of early leaks.
- EnterpriseProtect confidential videos, training materials, and internal communications from insider leaks.
- Legal EvidenceProvide forensic proof in court or contract disputes about who violated NDAs or distribution agreements.
- Brand ProtectionIPrevent unauthorized distribution that damages your brand reputation and market value.
- Revenue ProtectionStop revenue loss from piracy by identifying and eliminating leak sources quickly.
The Complete Leak Tracing Process
Distribution Source Setup
Each distribution point (partner, region, client group) receives content with a unique watermark identifier embedded invisibly into the video.
Content Distribution
Watermarked content is distributed to clients. Each client receives the same content but with their source’s unique watermark.
Continuous Monitoring
Our system continuously scans piracy sites, social media, and file-sharing platforms for your content.
Leak Detection
When leaked content is found, the watermark is automatically extracted and analyzed.
Source Identification
The watermark reveals which distribution source and specific client was responsible for the leak.
Actionable Intelligence
Receive detailed reports with forensic evidence to take legal action, terminate contracts, or strengthen security.
What You Get
- Exact identification of leak sources at the client level
- Real-time alerts when leaks are detected
- Integration with existing content delivery workflows
- Tamper-proof technology that survives re-encoding
- Forensic-grade evidence for legal proceedings
- Detailed analytics on leak patterns and trends
- Invisible watermarks that don't affect viewing quality
- Scalable solution for high-volume distribution
Lock Down Your Media Revenue
Stop bleeding subscription revenue to offshore piracy rings. Deploy WebKyte Intelligence natively within 48 hours.
Stop Content Leaks Today
Protect your content and identify leak sources with precision leak tracing technology.